Introduction
The recognition of advancements in quantum communication and cryptography through the 2025 ACM A.M. Turing Award marks a structural shift in how the field is perceived. Work that originated as theoretical physics and information science now underpins emerging secure communication systems and long-term data protection strategies.
The award to Charles H. Bennett and Gilles Brassard acknowledges foundational contributions that continue to influence system design decisions today. Their work on the BB84 protocol defined the operational principles of quantum key distribution and established a new security model based on physical laws rather than computational assumptions.[1]
For engineering-led organisations, the significance lies not in the award itself, but in what it signals. Quantum communication is moving from isolated research programmes into system-level integration, where constraints, interoperability, and verification become dominant concerns. National initiatives and industry programmes increasingly position quantum technologies as part of future secure infrastructure, reinforcing the transition from theoretical constructs to deployable systems [2].
Key Learning Points
| Key learning point | Link to detailed explanation | External reference |
| BB84 established the foundation of quantum-secure communication | BB84 and the Foundations of Quantum Cryptography | [1] |
| Quantum communication is transitioning from theory to deployment | From Theory to Deployment: Quantum Communication Systems | [2] |
| Industry momentum is driven by both research recognition and funding | Industry Momentum: Recognition, Investment, and Scale | [3] |
| Photonics and hardware constraints remain key scaling challenges | System-Level Constraints and Engineering Trade-offs | [4] |
| Quantum networking introduces new verification and integration challenges | Implications for System Architecture and Verification | [5] |
BB84 and the Foundations of Quantum Cryptography
The BB84 protocol, introduced by Charles H. Bennett and Gilles Brassard in 1984, established the first practical framework for secure key exchange using quantum mechanics. It encodes information in quantum states, typically via photon polarisation, in which the act of measurement irreversibly alters the state. This behaviour is not an implementation artefact but a direct consequence of quantum mechanics, which ensures that any observation of the transmitted signal introduces detectable changes. As a result, the protocol enables two parties to identify the presence of an eavesdropper by analysing discrepancies in measurement outcomes, forming the basis of quantum key distribution systems [1].
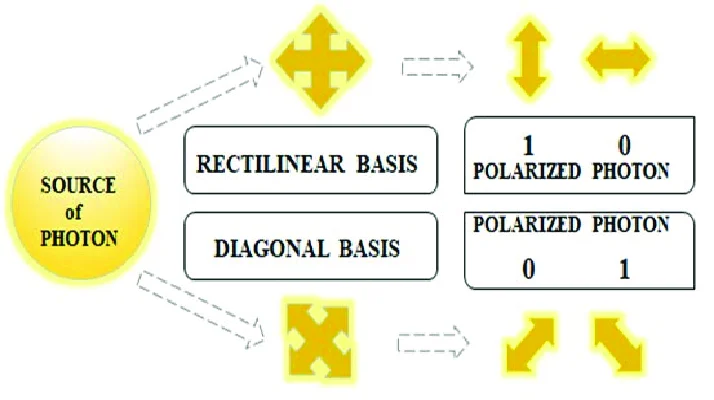
Fig 1: Basis and polarised states used for the BB84 protocol. Source: researchgate.net
Figure 1 shows how BB84 uses non-orthogonal bases, with the sender and receiver selecting measurement bases independently and retaining only aligned results. Any interception introduces detectable discrepancies, forming the basis of quantum key distribution.
From a system perspective, BB84 shifts security from computational assumptions to physical principles. However, it introduces engineering constraints across photon generation, detection, and synchronisation, with performance directly dependent on noise, loss, and hardware fidelity. These factors define the practical limits of quantum communication systems [3].
From Theory to Deployment: Quantum Communication Systems
Quantum communication is transitioning from research to early deployment, introducing practical engineering constraints. These systems are inherently hybrid, combining quantum transmission with classical control layers for reconciliation, error correction, and key management, all tightly coupled through timing and synchronisation dependencies [3].
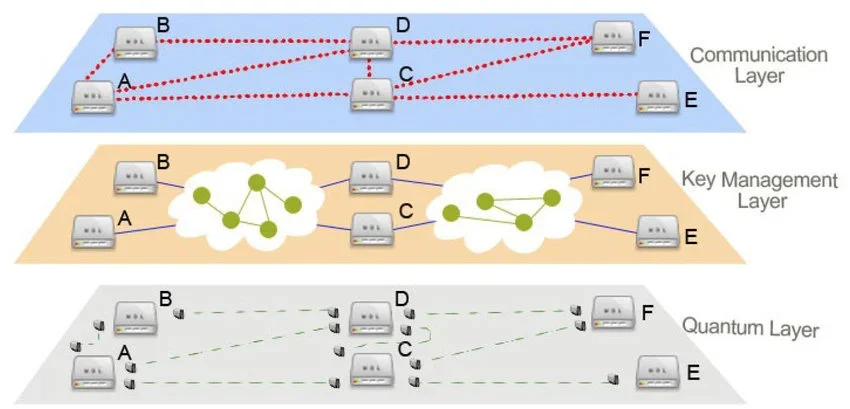
Fig 2: QKD network hierarchy with quantum, key management, and communication (key usage) layers. Source: researchgate.net
Figure 2 shows a layered QKD architecture, where the quantum layer handles photon transmission and detection, the key management layer performs processing and coordination, and the communication layer enables secure data exchange. System performance depends on stable interaction across these layers, with latency, noise, and channel conditions directly affecting key generation efficiency and reliability.
Deployment challenges include fibre attenuation, environmental noise, and integration with existing infrastructure. Quantum repeaters remain immature, limiting long-distance scalability, while satellite-based approaches introduce constraints in alignment, timing, and atmospheric effects [2][3].
These systems do not replace classical networks but extend them. Effective deployment, therefore, requires co-design across photonics, electronics, and network layers to ensure reliable operation.
Industry Momentum: Recognition, Investment, and Scale
The 2025 Turing Award reflects a broader pattern of recognition across the quantum ecosystem. Multiple awards and funding initiatives indicate increasing alignment between academic research and industrial priorities.
Recent developments include:
- Recognition of quantum phenomena in major physics awards
- Advances in quantum simulation and communication research
- Growth in photonic quantum computing platforms
Companies such as Quandela and XeedQ are exploring scalable implementations, while Sateliot focuses on secure communication infrastructure.
This activity reflects three converging trends:
- Increased availability of venture and public funding
- Strategic interest in secure communication infrastructure
- Maturation of enabling technologies such as photonics and cryogenic electronics
The presence of investment does not imply immediate scalability. Instead, it indicates that organisations expect long-term system integration challenges to be resolved incrementally.
Broader trends in emerging technologies and system evolution are also evident in quantum EDA engineering at scale.
System-Level Constraints and Engineering Trade-offs
Quantum communication systems are fundamentally constrained by physical limits in quantum state transmission. Optical loss, noise, and decoherence reduce the photon detection probability and increase error rates, thereby directly limiting distance, reliability, and key-generation efficiency. These constraints define system performance boundaries and must be addressed during design rather than post-deployment [4].
Similar programme-level risks in verification and system delivery are observed in large-scale engineering systems, where constraints must be addressed at the design stage rather than post-deployment.
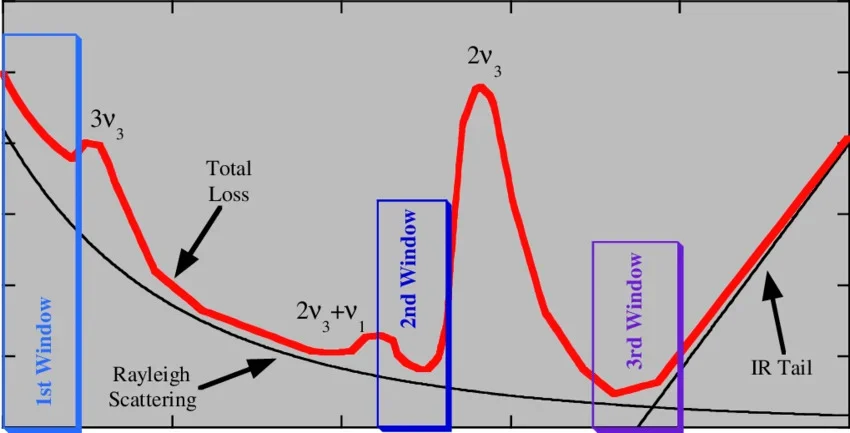
Fig 3: Attenuation vs. wavelength curve for a standard silica optical fibre. Source: researchgate.net
Figure 3 shows how attenuation and scattering accumulate across optical channels. Unlike classical systems, signal amplification is not viable without disrupting quantum states, making loss a fundamental constraint. This drives the need for high-efficiency detectors, low-loss channels, and future repeater architectures [4][5].
Key trade-offs include:
- Distance vs reliability: Longer channels increase loss and error rates
- Security vs throughput: Stricter thresholds reduce usable key rates
- Hardware fidelity vs cost: High-performance components remain expensive
- Integration vs isolation: Systems must balance noise isolation with real-world deployment
These constraints reflect broader system-level risks in engineering programmes. Effective solutions require co-design at the architecture stage, as retrofitting typically leads to suboptimal performance.
Implications for System Architecture and Verification
Quantum communication fundamentally shifts verification from deterministic correctness to probabilistic behaviour driven by measurements of quantum states. Unlike classical systems with repeatable outputs, quantum systems yield statistical outcomes that are influenced by noise, loss, and device imperfections.
These challenges are consistent with broader system-level verification complexity in modern architectures, where interactions between subsystems define overall system behaviour.
This requires hybrid modelling approaches that combine quantum physics with classical control to capture effects such as channel attenuation, detector efficiency, and stochastic errors. Without sufficient modelling fidelity, verification results cannot be correlated with real-world system performance or security guarantees.
Verification must therefore extend beyond functional checks to include statistical validation, error thresholds, and long-duration analysis. At the system level, interface validation is critical due to the tight coupling between quantum and classical subsystems, which imposes strict timing and synchronisation requirements.
In addition, the lack of standardisation introduces interoperability risks across implementations. As a result, verification frameworks must evolve through co-simulation, hardware-in-the-loop testing, and cross-domain strategies to achieve reliable system-level confidence.
Conclusion
The 2025 Turing Award recognises work that has already influenced system design across secure communication domains. The BB84 protocol remains a reference point for quantum cryptography, but its practical implementation exposes a wide range of engineering challenges.
Quantum communication is not a single technology transition. It is a system-level evolution that requires coordination across:
- Photonics and semiconductor design
- Network architecture and infrastructure
- Verification methodologies and standards
The current phase reflects early deployment rather than maturity. Recognition and investment indicate direction, not completion. For technical decision-makers, the priority is to understand constraints, validate assumptions, and integrate quantum capabilities where they provide measurable value.
For more insights on quantum systems, communication architectures, and emerging quantum technologies, explore our Quantum blog category.
References
[1] ACM A.M. Turing Award – https://awards.acm.org/about/2025-turing
[2] National Quantum Initiative – https://www.quantum.gov
[3] IBM Quantum – https://www.ibm.com/quantum
[4] IEEE – https://ieee.org
[5] Nature Quantum Information – https://www.nature.com

Written by : Mike Bartley
Mike started in software testing in 1988 after completing a PhD in Math, moving to semiconductor Design Verification (DV) in 1994, verifying designs (on Silicon and FPGA) going into commercial and safety-related sectors such as mobile phones, automotive, comms, cloud/data servers, and Artificial Intelligence. Mike built and managed state-of-the-art DV teams inside several companies, specialising in CPU verification.
Mike founded and grew a DV services company to 450+ engineers globally, successfully delivering services and solutions to over 50+ clients.
Mike started Alpinum in April 2025 to deliver a range of start-of-the art industry solutions:
Alpinum AI provides tools and automations using Artificial Intelligence to help companies reduce development costs (by up to 90%!) Alpinum Services provides RTL to GDS VLSI services from nearshore and offshore centres in Vietnam, India, Egypt, Eastern Europe, Mexico and Costa Rica. Alpinum Consulting also provides strategic board level consultancy services, helping companies to grow. Alpinum training department provides self-paced, fully online training in System Verilog, UVM Introduction and Advanced, Formal Verification, DV methodologies for SV, UVM, VHDL and OSVVM and CPU/RISC-V. Alpinum Events organises a number of free-to-attend industry events
You can contact Mike (mike@alpinumconsulting.com or +44 7796 307958) or book a meeting with Mike using Calendly (https://calendly.com/mike-alpinum-consulting).
Stay Informed and Stay Ahead
Latest Articles, Guides and News
Explore related insights from Alpinum that dive deeper into design verification challenges, practical solutions, and expert perspectives from across the global engineering landscape.