Introduction
The transition toward open instruction set architectures is reshaping modern semiconductor development. Among these, RISC-V has moved from academic exploration into commercial deployment across embedded systems, automotive platforms, AI accelerators, and general-purpose compute devices. As architectural flexibility increases, verification responsibility expands accordingly.
RISC-V verification training , therefore, becomes a system-level concern rather than a narrow technical activity. Verification determines whether configurable processor implementations, memory hierarchies, and interconnect behaviour align with architectural intent under real operating conditions. When verification capability lags architectural ambition, delivery schedules and product confidence are directly affected.
This article examines the technical forces behind rising verification demand, the structural skills gap emerging across engineering teams, and the role of structured learning in restoring verification certainty.
Five Key Learning Points
| Key learning point | Link to detailed explanation | External reference |
| RISC-V adoption is accelerating across multiple SoC domains | RISC-V Adoption and System Impact | https://riscv.org |
| Verification complexity increases in open ISA ecosystems | Verification Complexity in Open ISA Systems | https://ieeexplore.ieee.org |
| Skills shortages create programme-level delivery risk | The Verification Skills Gap | https://semiengineering.com |
| Structured verification methodology reduces uncertainty | Structured Verification Methodologies for RISC-V | https://accellera.org |
| Focused training improves verification readiness and confidence | Why Focused RISC-V Verification Training Matters | https://riscv.org |
RISC-V Adoption and System Impact
RISC-V adoption is driven by architectural openness, extensibility, and ecosystem momentum. Unlike fixed proprietary ISAs, RISC-V enables domain-specific customisation at the instruction, microarchitectural, and subsystem levels. This flexibility supports optimisation for:
- Ultra-low-power embedded control
- Safety-critical automotive processing
- AI and vector acceleration
- Secure edge computing
However, configurability introduces verification variability. Each architectural extension, privilege configuration, or memory protection scheme alters the verification state space. Programmes must therefore validate not only the correctness of a reference core but also that of each configured implementation .
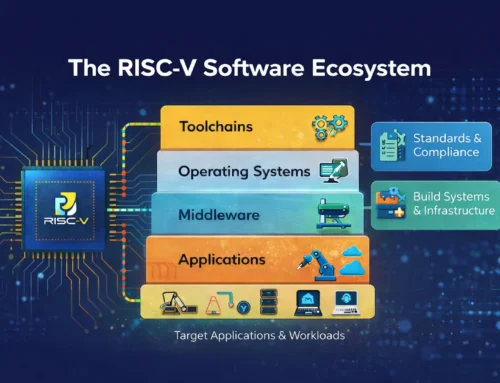
From a system perspective, this expands verification from component testing to architectural assurance across firmware, operating systems, and heterogeneous compute domains.
Verification Complexity in Open ISA Systems
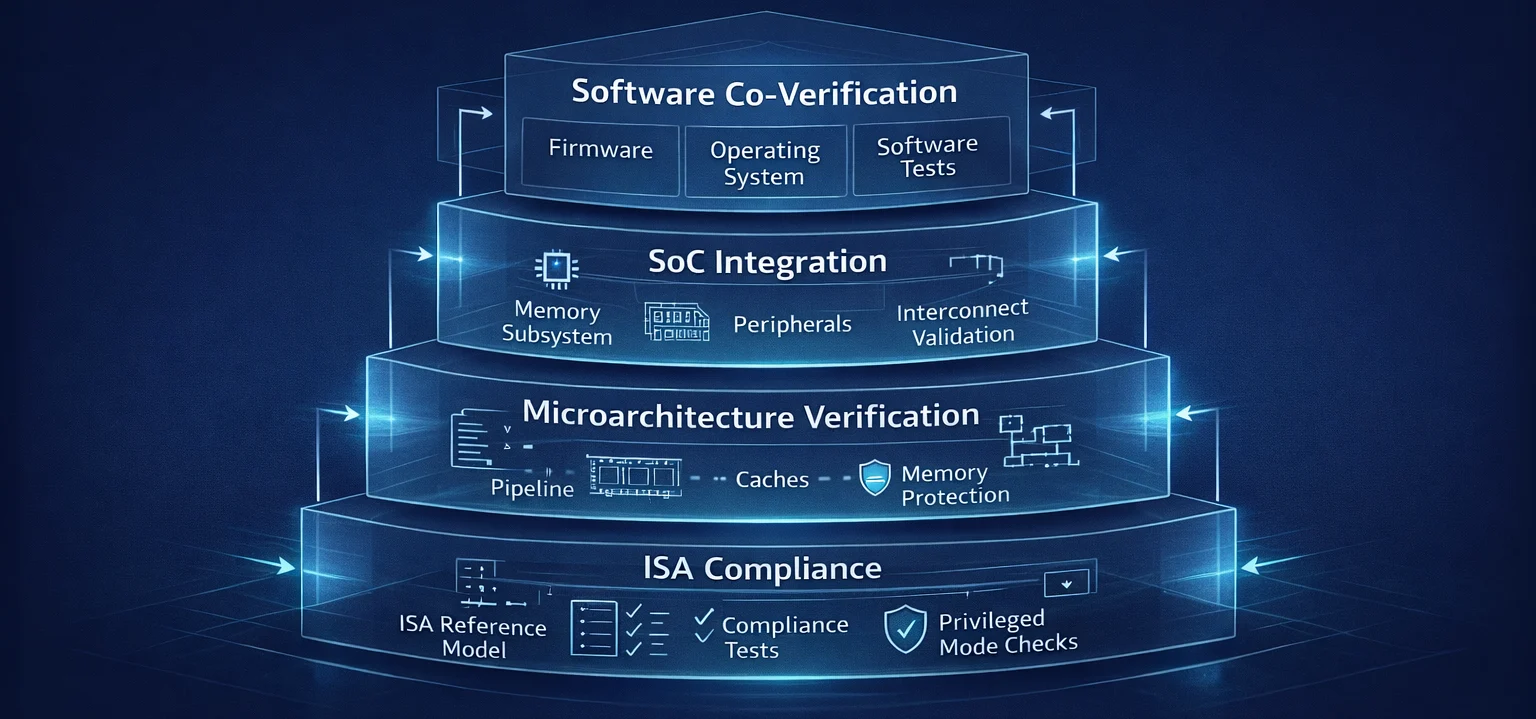
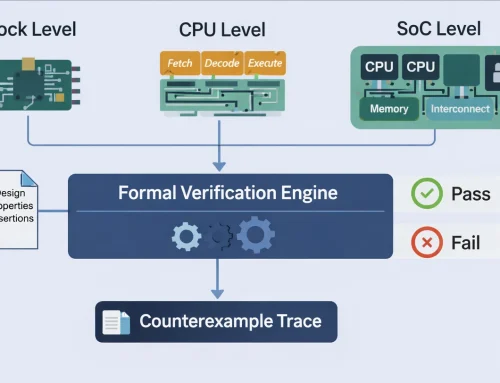
Open ISAs introduce verification challenges that differ from traditional fixed-architecture processors. Figure 1 illustrates that verification responsibility in configurable RISC-V systems extends beyond RTL functional correctness into full-system execution behaviour. Each additional layer introduces new architectural states, interaction paths, and software dependencies that must be validated to achieve delivery confidence.
This layered expansion explains why verification effort grows non-linearly as designs move from core implementation to integrated SoC deployment.
Figure 1: RISC-V System Verification Stack
Figure 1 illustrates a layered verification view spanning ISA compliance, microarchitecture behaviour, SoC integration, and software co-verification.
Configuration explosion
Optional extensions, privilege modes, and custom instructions increase the number of verification scenarios. Test completeness becomes harder to define because architectural boundaries are flexible rather than fixed.
Microarchitectural diversity
Different implementations of the same ISA may vary in pipeline depth, cache topology, or coherence strategy. Functional compliance alone is insufficient. Timing, ordering, and interaction behaviour must also be validated.
Software-hardware interaction
Boot code, compilers, and operating systems interact closely with RISC-V privilege and memory models. Verification must therefore include firmware and software execution paths, not only RTL correctness.
Compliance versus correctness
ISA compliance suites verify specification adherence but do not guarantee absence of corner-case failures in complex SoC environments. Additional constrained random, formal, and scenario-based verification remains necessary.
These factors increase both verification workload and expertise requirements. Without a structured methodology, verification effort scales unpredictably.
The Verification Skills Gap
Demand expansion across the industry
As commercial RISC-V deployments increase, organisations require engineers capable of:
- Understanding ISA semantics and privilege architecture
- Building verification environments for configurable cores
- Interpreting compliance, coverage, and formal results
- Debugging cross-layer failures involving RTL and software
Industry hiring trends indicate that such combined architectural and verification expertise is limited relative to demand.
Programme-level consequences
When verification capability is insufficient:
- Coverage closure is delayed
- Corner-case failures escape into silicon
- Software integration exposes latent defects
- Confidence in tape-out readiness declines
These outcomes affect cost, schedule, and system reliability, not just engineering workload.
Structured Verification Methodologies for RISC-V
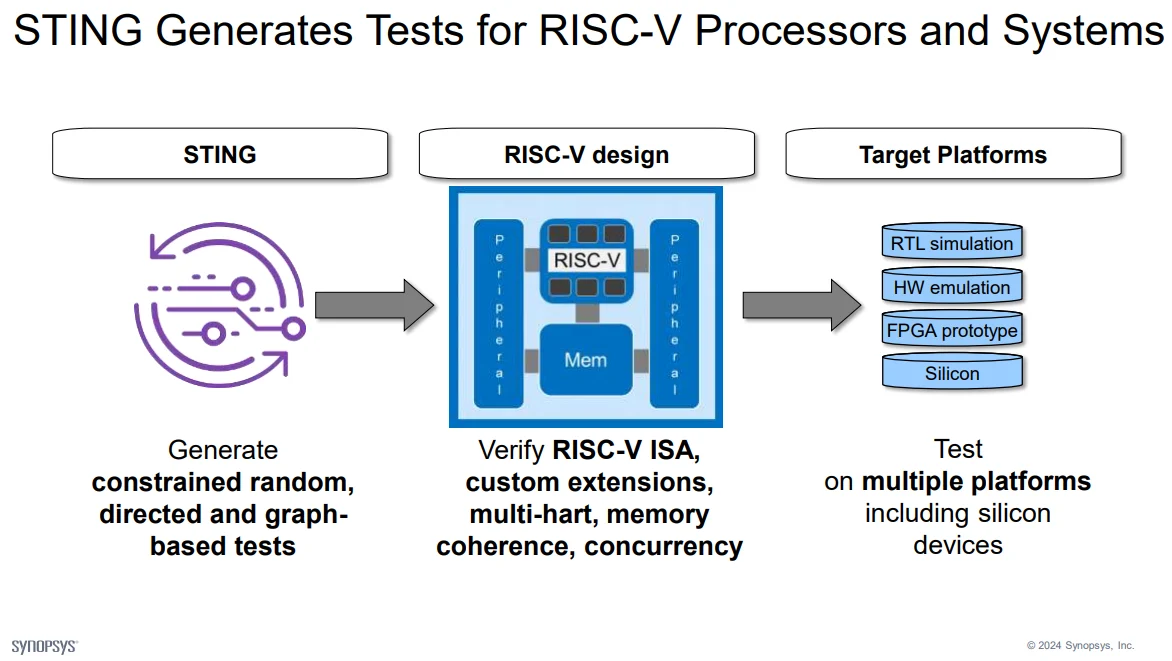
A disciplined verification approach reduces uncertainty introduced by configurability. Figure 2 illustrates that verification confidence is achieved through progressive validation across environments, rather than reliance on a single verification stage. Automated stimulus generation exercises ISA behaviour, custom extensions, memory coherence, and concurrency. At the same time, execution on increasingly realistic platforms exposes timing, integration, and software-interaction effects that are not visible in simulation alone.
Figure 2: Verification Methodology Flow for Configurable RISC-V Cores
Figure 2 illustrates the flow from constrained-random and directed stimulus generation through architectural verification to execution across simulation, emulation, FPGA prototyping, and silicon platforms.
ISA compliance as baseline
Compliance testing establishes conformance to architectural specifications. It provides an entry point but not full assurance.
Constrained random and coverage analysis
Scenario diversity is achieved through constrained stimulus generation and functional coverage measurement. Coverage metrics guide verification completeness.
Formal verification for corner cases
Formal techniques explore unreachable simulation states and validate safety properties such as privilege isolation and memory protection.
Co-verification with software
Running firmware and operating systems within verification environments exposes integration defects early in development.
Continuous regression and automation
Automated regression ensures configuration variants remain validated as RTL evolves.
Together, these practices transform verification from ad hoc testing into an engineering system that scales with architectural flexibility.
Why Focused RISC-V Verification Training Matters
Verification effectiveness depends on shared technical understanding across engineering teams. Focused learning contributes in several ways.
Alignment of architectural interpretation
Training clarifies ISA semantics, privilege behaviour, and extension interaction. Misinterpretation at this level often leads to subtle verification gaps.
Methodology consistency
Engineers apply consistent approaches to coverage, stimulus generation, and debugging. This reduces variability between projects and teams.
Faster problem diagnosis
Understanding verification theory alongside practical tooling enables earlier identification of root causes rather than symptomatic debugging.
Reduced programme risk
Improved verification capability strengthens confidence in tape-out readiness and long-term maintainability.
From a systems viewpoint, training functions as risk-mitigation infrastructure, not merely asknowledge transfer.
Conclusion
RISC-V adoption is transforming processor design through openness and configurability. This transformation increases verification responsibility across architectural, microarchitectural, and software layers.
Where verification expertise does not evolve at the same pace, programme-level risks emerge in coverage closure, silicon quality, and delivery certainty. Structured methodology and focused learning provide practical ways to restore verification confidence.
Understanding verification as a system capability rather than an isolated activity is therefore central to successful RISC-V deployment.
Access to Structured RISC-V Verification Learning
Engineers and technical leaders who require a deeper, methodical understanding of verification practices in configurable RISC-V processor environments may review the structured technical outline of the training programme described here:
RISC-V Verification Training Overview
https://alpinumconsulting.com/services/training/riscv-verification-training/
This course outline explains the architectural scope, the coverage of verification methodologies, and the practical engineering context addressed in the programme.
For those who have reviewed the technical details and wish to participate in the upcoming session, registration information is available here:
Training Registration
https://www.tickettailor.com/events/alpinumconsulting/2075231

Written by : Mike Bartley
Mike started in software testing in 1988 after completing a PhD in Math, moving to semiconductor Design Verification (DV) in 1994, verifying designs (on Silicon and FPGA) going into commercial and safety-related sectors such as mobile phones, automotive, comms, cloud/data servers, and Artificial Intelligence. Mike built and managed state-of-the-art DV teams inside several companies, specialising in CPU verification.
Mike founded and grew a DV services company to 450+ engineers globally, successfully delivering services and solutions to over 50+ clients.
Mike started Alpinum in April 2025 to deliver a range of start-of-the art industry solutions:
Alpinum AI provides tools and automations using Artificial Intelligence to help companies reduce development costs (by up to 90%!) Alpinum Services provides RTL to GDS VLSI services from nearshore and offshore centres in Vietnam, India, Egypt, Eastern Europe, Mexico and Costa Rica. Alpinum Consulting also provides strategic board level consultancy services, helping companies to grow. Alpinum training department provides self-paced, fully online training in System Verilog, UVM Introduction and Advanced, Formal Verification, DV methodologies for SV, UVM, VHDL and OSVVM and CPU/RISC-V. Alpinum Events organises a number of free-to-attend industry events
You can contact Mike (mike@alpinumconsulting.com or +44 7796 307958) or book a meeting with Mike using Calendly (https://calendly.com/mike-alpinumconsulting).
Stay Informed and Stay Ahead
Latest Articles, Guides and News
Explore related insights from Alpinum that dive deeper into design verification challenges, practical solutions, and expert perspectives from across the global engineering landscape.