The growth of open processor architectures has significantly increased the adoption of RISC‑V across embedded systems, AI accelerators, and high-performance computing platforms. This flexibility allows engineering teams to design processors with highly customised instruction sets and microarchitectures. However, this flexibility also increases verification complexity.
Traditional simulation-based verification remains essential. Nevertheless, the scale of modern processors means that simulation alone often struggles to expose corner-case behaviour in instruction pipelines, privilege handling, memory ordering, or security enforcement mechanisms.
For this reason, formal verification in RISC-V verification has become an increasingly important technique. Formal methods enable engineers to mathematically prove design properties and explore state spaces that are difficult to reach through simulation alone.
In practice, formal verification can be applied at several levels of processor design:
- Block level
- CPU level
- System or SoC level
- Safety and security verification applications
Each level presents different verification challenges and requires different modelling strategies.
Five Key Learning Points
| Key learning point | Link to detailed explanation | External reference |
| Why formal verification matters in modern RISC-V processor development | Why formal verification is increasingly relevant in RISC-V verification | [2] |
| Applying formal verification at block level | Block-level formal verification for RISC-V components | [1] |
| CPU-level formal verification of processor pipelines and instruction behaviour | CPU-level formal verification in RISC-V processors | [4] |
| Using formal verification for SoC-level safety and security | Formal verification at system and SoC level | [3] |
| Integrating formal verification into verification workflows | Integrating formal verification into a RISC-V verification strategy | [1] |
Why Formal Verification is Increasingly Relevant in RISC-V Verification
Modern processor verification faces a combination of factors:
- Highly configurable instruction sets
- Deep execution pipelines
- Multiple privilege modes
- Complex memory systems
- Increasing safety and security requirements
These challenges are particularly visible in configurable architectures such as RISC‑V, where implementers may add custom instructions, accelerators, or specialised privilege extensions.
Simulation is effective at validating typical software scenarios. However, it often struggles to guarantee coverage of corner cases such as:
- Pipeline hazards
- Interrupt timing
- Privilege transitions
- Cache coherence states
- Security boundary violations
Formal verification addresses this limitation by analysing all reachable states within a defined model.
Organisations such as Accellera Systems Initiative have contributed significantly to formal verification methodology development, particularly through SystemVerilog assertions and property-based verification approaches [1].
When used appropriately, formal methods allow verification teams to:
- Prove correctness properties
- Detect unreachable states
- Identify deadlock conditions
- Verify protocol compliance
These capabilities complement simulation rather than replacing it.
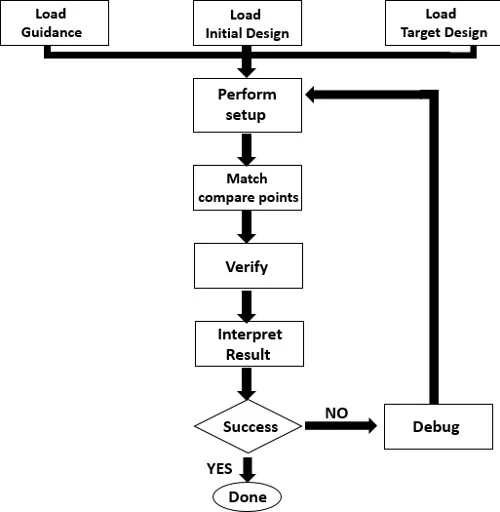
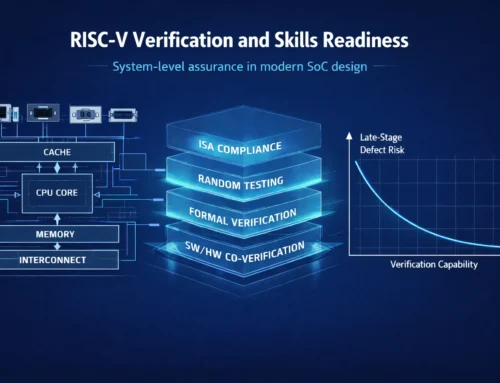
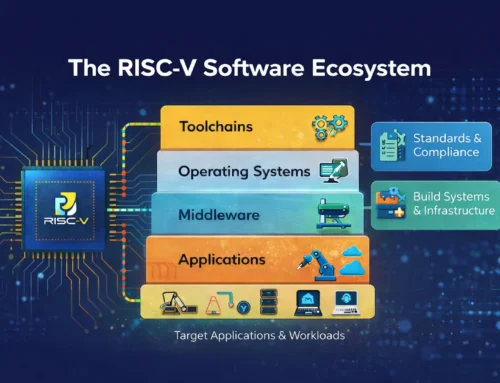
Modern processor verification rarely relies on a single technique. Instead, teams combine architectural modelling, simulation, constrained random verification, and formal analysis. The challenge is coordinating these techniques so that architectural intent, implementation behaviour, and verification evidence remain aligned throughout the programme. Figure 1 illustrates a simplified verification framework used in many processor development flows.
Figure 1: Multi-Level Verification Framework. Source: embeddedcomputing
Formal verification engines explore the state space defined by the design and property constraints. When a property fails, the tool generates a counterexample trace that shows how the violation occurs. This trace can often expose subtle bugs that simulation may miss.
Block-Level Formal Verification for RISC-V Components
Block-level formal verification typically focuses on individual modules within a processor design. Examples include:
- Instruction decoders
- ALU units
- Register files
- Pipeline control logic
- bus interfaces
At this level, formal verification is particularly effective because the state space remains manageable.
Engineers typically write properties using SystemVerilog Assertions (SVA) to specify behavioural constraints. Examples include:
- Instruction decode correctness
- Register write consistency
- Hazard detection behaviour
- Protocol compliance on interconnect interfaces
These checks are useful for identifying structural errors early in development. For example, a property might ensure that register zero in a RISC-V implementation always reads as zero, regardless of instruction behaviour. This requirement appears simple, yet implementation errors in writeback logic can violate it under rare timing conditions.
Formal verification can detect such issues early, often before simulation environments are fully operational.
CPU-Level Formal Verification in RISC-V Processors
When moving from block-level to CPU-level verification, complexity increases significantly.
At CPU level, verification must consider:
- Pipeline interactions
- Instruction ordering
- Branch prediction behaviour
- Exception handling
- Interrupt timing
One commonly used technique is instruction-level formal verification. In this approach, properties are written to ensure that each instruction produces the correct architectural state. For example, engineers may verify:
- Arithmetic instruction correctness
- Branch target behaviour
- Privilege transitions
- CSR register updates
Instruction-level formal verification often uses reference models derived from the architectural specification.
The RISC‑V International specification defines precise architectural behaviour for instructions, privilege modes, and memory models [2]. These specifications provide a foundation for formal property definition.
However, CPU-level formal verification can become computationally expensive if constraints are poorly defined. Careful abstraction and decomposition are therefore essential.
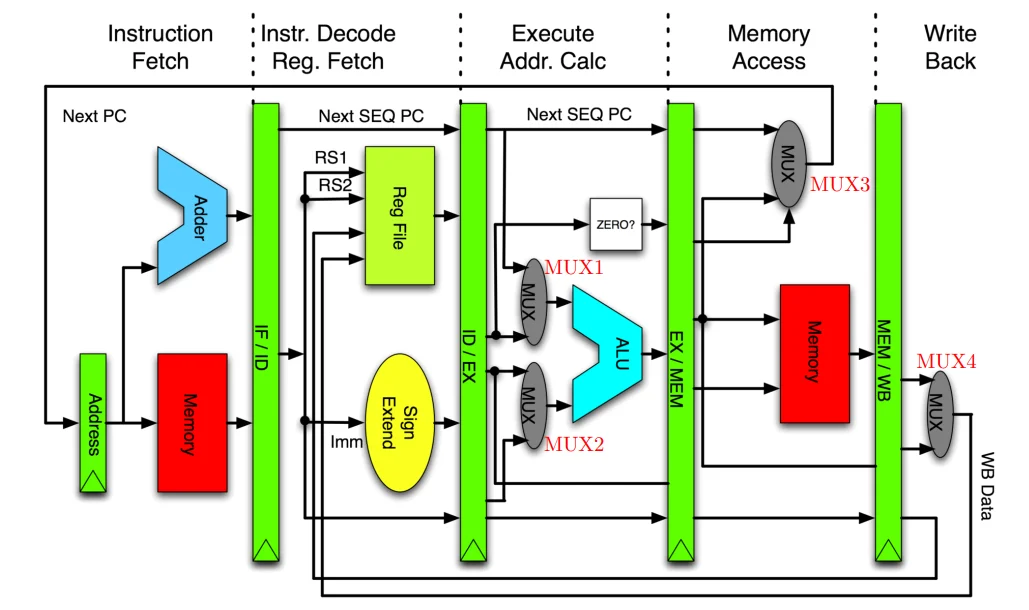
At CPU level, verification must consider the interaction between pipeline stages and the architectural state of the processor. Instructions pass through several stages including instruction fetch, decode, execution, and writeback. Verification must ensure that instructions produce correct architectural results even when hazards, interrupts, or privilege transitions occur. Figure 2 illustrates a simplified processor pipeline used as a conceptual model for CPU-level verification.
Figure 2: CPU Pipeline Verification Model. Source: stackoverflow.
Formal verification helps detect pipeline hazards such as:
- Data hazards
- Control hazards
- Incorrect forwarding logic
- Mis-handled exceptions
These behaviours may only occur under very specific conditions, making them difficult to detect through simulation alone.
Formal Verification at System and SoC Level
At the system level, verification scope expands beyond the processor core itself. Modern systems often integrate:
- Multiple CPU cores
- Accelerators
- Memory subsystems
- Interconnect fabrics
- Security controllers
Formal verification can be applied to ensure correct behaviour across these components. Typical applications include:
- Cache coherence protocol verification
- Interconnect protocol compliance
- Deadlock detection
- Security isolation verification
Projects such as lowRISC have demonstrated the use of formal verification techniques within open hardware platforms [3].
Safety-critical systems, such as automotive controllers, increasingly require formal verification to support certification standards. Formal analysis helps demonstrate that specific fault conditions cannot lead to unsafe system behaviour.
Similarly, security-oriented formal verification can verify properties such as:
- Privilege boundary enforcement
- Secure boot state transitions
- Memory protection behaviour
These applications are particularly relevant for SoC designs used in secure or safety-critical environments.
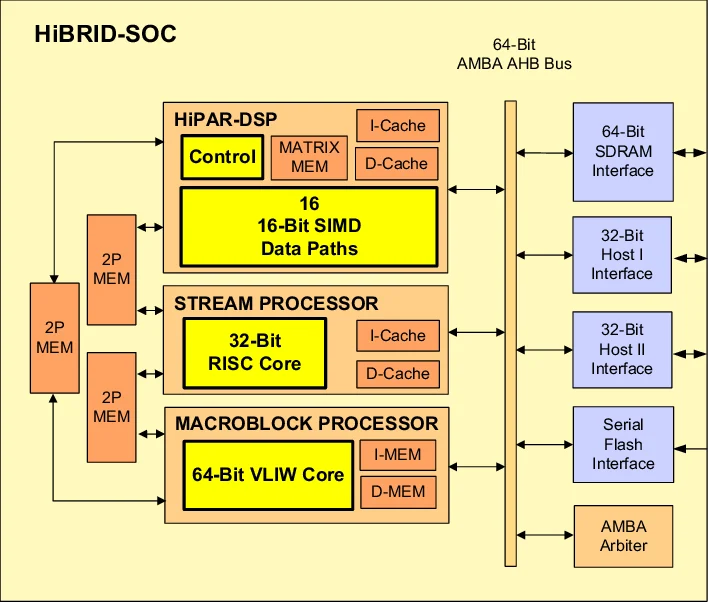
System-level verification extends beyond the processor core to include interactions between CPUs, memory hierarchies, interconnect fabrics, and peripheral subsystems. These interactions introduce additional verification challenges because faults may emerge from rare combinations of transactions across multiple components. Figure 3 illustrates a conceptual view of a modern system-on-chip architecture where multiple functional blocks interact through shared interconnect and memory subsystems.
Figure 3: Formal Verification at SoC Level. Source: researchgate
Formal verification tools can detect protocol violations or deadlocks that arise from rare interactions between components. Such issues are often extremely difficult to reproduce using simulation.
Integrating Formal Verification into a RISC-V Verification Strategy
Formal verification is most effective when integrated with simulation and other verification techniques.
A balanced verification strategy typically includes:
- Simulation regression testing
- Constrained random verification
- Formal property checking
- Coverage analysis
- Architectural modelling
Formal verification tends to be most effective when used for:
- Critical control logic
- Architectural correctness
- Safety-critical behaviours
- Security properties
However, formal methods require careful planning. Poorly constrained models can lead to state-space explosion, where analysis becomes computationally infeasible. Verification teams therefore often combine:
- Bounded model checking
- Abstraction techniques
- Compositional verification
These approaches help keep the problem manageable while maintaining useful verification coverage. For RISC-V processors in particular, the combination of architectural flexibility and modular extensions makes a structured verification strategy essential.
Conclusion
Formal verification has become an important component of modern processor verification strategies. In RISC-V verification, its value lies in the ability to analyse behaviours that simulation alone may not reliably explore.
- At block level, formal verification helps validate control logic and protocol compliance.
- At CPU level, it enables verification of instruction behaviour and pipeline interactions.
- At system level, it supports safety and security verification across complex SoC architectures.
When integrated with simulation and coverage-driven verification, formal methods can significantly improve verification confidence in processor development programmes.
Further Learning and Technical Discussion
Engineers interested in deeper discussion of formal verification in RISC-V verification may find the following resources useful:
- Training resources available through Alpinum Consulting
https://alpinumconsulting.com/services/training/ - Technical events including DVClub
https://alpinumconsulting.com/events/dvclub/ - Verification conferences such as Verification Futures
https://alpinumconsulting.com/verification-futures/
These forums provide opportunities to explore emerging verification techniques and practical engineering experiences across the semiconductor industry.
References
[1] Accellera Systems Initiative – Formal Verification and SystemVerilog Assertions
https://www.accellera.org
[2] RISC-V Instruction Set Architecture Specification
https://riscv.org
[3] lowRISC Open Silicon Project
https://lowrisc.org
[4] IEEE – Institute of Electrical and Electronics Engineers
https://ieee.org

Written by : Mike Bartley
Mike started in software testing in 1988 after completing a PhD in Math, moving to semiconductor Design Verification (DV) in 1994, verifying designs (on Silicon and FPGA) going into commercial and safety-related sectors such as mobile phones, automotive, comms, cloud/data servers, and Artificial Intelligence. Mike built and managed state-of-the-art DV teams inside several companies, specialising in CPU verification.
Mike founded and grew a DV services company to 450+ engineers globally, successfully delivering services and solutions to over 50+ clients.
Mike started Alpinum in April 2025 to deliver a range of start-of-the art industry solutions:
Alpinum AI provides tools and automations using Artificial Intelligence to help companies reduce development costs (by up to 90%!) Alpinum Services provides RTL to GDS VLSI services from nearshore and offshore centres in Vietnam, India, Egypt, Eastern Europe, Mexico and Costa Rica. Alpinum Consulting also provides strategic board level consultancy services, helping companies to grow. Alpinum training department provides self-paced, fully online training in System Verilog, UVM Introduction and Advanced, Formal Verification, DV methodologies for SV, UVM, VHDL and OSVVM and CPU/RISC-V. Alpinum Events organises a number of free-to-attend industry events
You can contact Mike (mike@alpinumconsulting.com or +44 7796 307958) or book a meeting with Mike using Calendly (https://calendly.com/mike-alpinumconsulting).
Connect With Us
We understand that you might have a unique situation that you would like to discuss with us, or just be curious to learn more about our service offerings. Regardless, we would like to hear from you – please feel free to contact us.
Stay Informed and Stay Ahead
Latest Articles, Guides and News
Explore related insights from Alpinum that dive deeper into design verification challenges, practical solutions, and expert perspectives from across the global engineering landscape.